Scaling the autonomous network: Introducing the Data Steward and Core Network Agents
Last year, Google Cloud unveiled the Autonomous Network Operations framework, a comprehensive blueprint designed to help Communication Service Provide...
Last year, Google Cloud unveiled the Autonomous Network Operations framework, a comprehensive blueprint designed to help Communication Service Provide...

Written by: Casey Charrier, James Sadowski, Zander Work, Clement Lecigne, Benoît Sevens, Fred Plan Executive Summary Google Threat Intelligence Group...
Creating precise, high-quality images often involves endless trial and error. You need a model that actually understands what you’re asking for. Buil...

When platform engineers, AI Infrastructure leads and developers think about autoscaling workloads running on Kubernetes, their goal is straightforward...
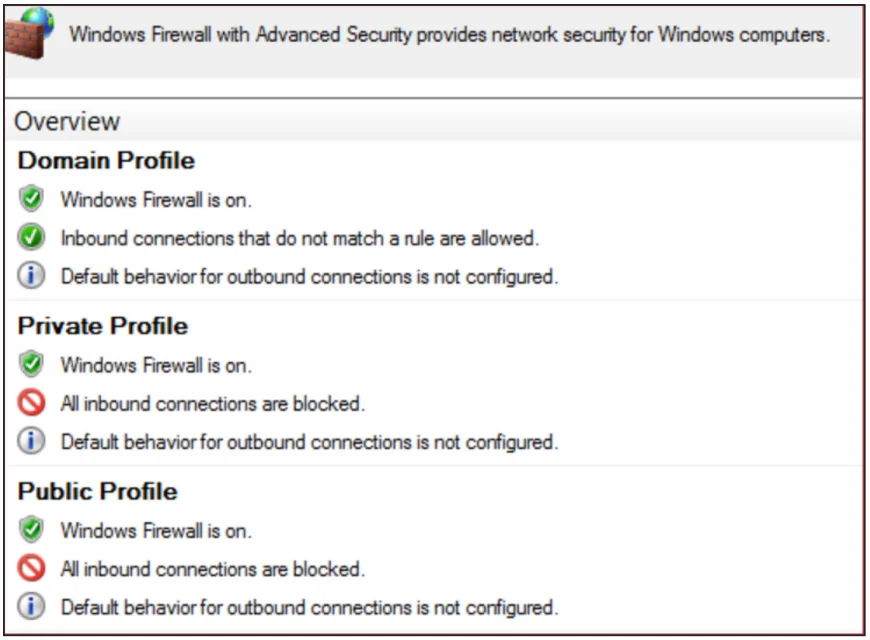
Written by: Matthew McWhirt, Bhavesh Dhake, Emilio Oropeza, Gautam Krishnan, Stuart Carrera, Greg Blaum, Michael Rudden Background Threat actors lever...

Want to know the latest from Google Cloud? Find it here in one handy location. Check back regularly for our newest updates, announcements, resources,...

Hey builders! Stop typing, and start interacting! We are moving beyond the text box. The future of AI is all about immersive, real-time experiences. T...

Discover how 43% of security leaders now use threat intelligence for strategic planning. Explore key insights from the 2025 State of Threat Intelligen...

Discover how threat intelligence has moved from the SOC to the boardroom. Learn why modern enterprises use it to drive strategic decisions, manage ris...

Explore the latest third-party risk statistics and learn how data-driven, continuous monitoring for third-party risk assessments can protect your supp...
Struggling with vulnerability overload? Learn why CVSS scores alone aren't enough—and how a three-pillar framework using real-world threat intel, envi...
Move beyond noise. Learn how to build effective threat intelligence operations that turn raw data into actionable insights and proactive cyber defense...
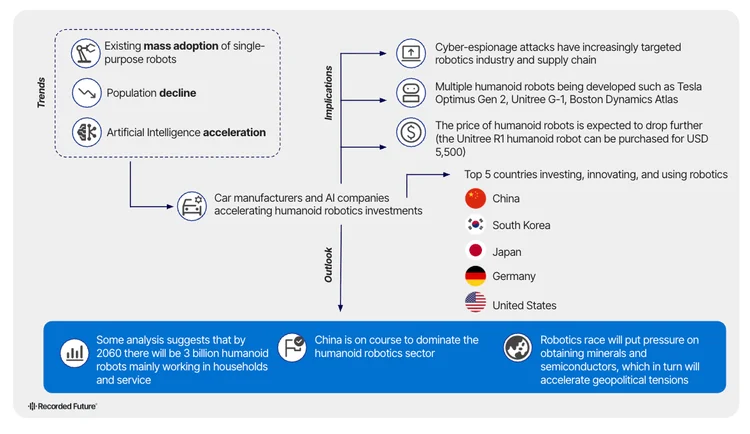
Humanoid robots are arriving faster than anyone expected. Discover the hidden risks, global power shifts, and breakthroughs shaping the future — befor...

Discover how threat intelligence automation from Recorded Future empowers security teams with real-time insights, faster response, and greater efficie...
Evaluating digital risk intelligence platforms? Learn the 5 essential capabilities you should consider in order to protect your brand, assets, and att...
Are you sure you want to sign out?