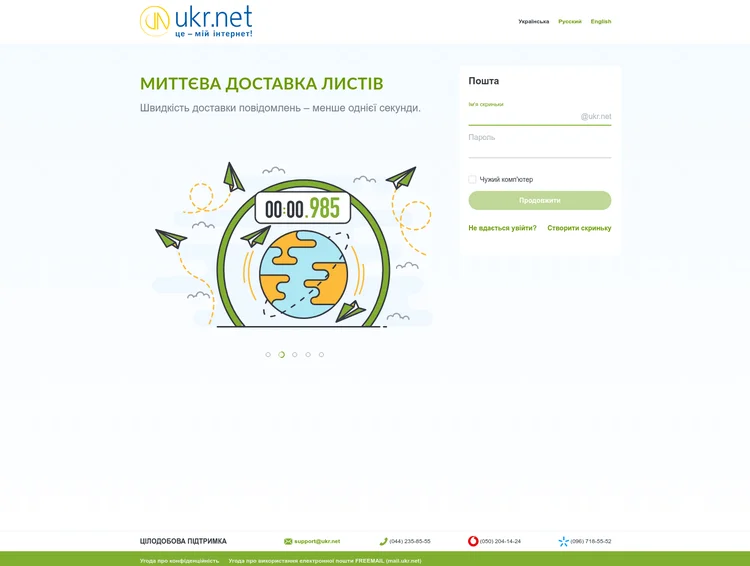
BlueDelta’s Persistent Campaign Against UKR.NET
Discover how Russia’s BlueDelta targets UKR.NET users with advanced credential-harvesting campaigns, evolving tradecraft, and multi-stage phishing tec...
Commercial real estate and office spaces
Discover how Russia’s BlueDelta targets UKR.NET users with advanced credential-harvesting campaigns, evolving tradecraft, and multi-stage phishing tec...

Top enterprise threat intelligence trends for 2026: AI-augmented CTI, unified platforms, workflow integration, data fusion, budgets, ROI, and maturity...

Explores Palestine Action’s post-designation global network, tactics, and targets, and evaluates key physical risks and mitigations for organizations.

Examines Russia-India-China trilateral cooperation, U.S. tariffs and sanctions, why a formal bloc is unlikely, and implications for governments and bu...
Explore 5 third-party risk examples, from vendor data breaches to supply chain attacks and learn how third-party risk management can prevent cyberatta...

November 2025 CVE landscape: 10 exploited critical vulnerabilities, a 69% drop from October, and why Fortinet and Samsung flaws need urgent patching.

Note: The analysis cut-off date for this report was November 10, 2025 Executive Summary Insikt Group continues to monitor GrayBravo (formerly tracked...

Discover how converged threat intelligence protects executives from deepfakes, doxxing, and cyber-enabled physical threats with Recorded Future.

Discover how law firm breaches expose decades of M&A intelligence, client data, and privileged strategy—and how to reduce cascading vendor risk be...
Explore a decade of deserialization vulnerabilities, from Java to React/Next.js CVEs, and learn how to harden apps and stay ahead with Recorded Future...

Learn what advanced threat intelligence maturity really means and how to close the gap between current capabilities and predictive, autonomous operati...
Uncover Intellexa’s global corporate web powering Predator spyware, front companies, and expanding targeting from civil society to executives worldwid...
Uncover how Russia’s CopyCop network uses AI-generated news and fake media sites to influence global audiences—and learn the key defenses against synt...
Learn how ransomware works, how it can impact operations, revenue, and brand reputation, and how to prevent ransomware from infecting your business.

A grounded look at AI malware: most threats sit at low maturity levels, with no verified autonomous BYOAI attacks. Learn what’s real, what’s hype, and...

Learn how threat intelligence identifies supply-chain compromise risks in SaaS integrations and how Recorded Future helps organizations defend against...

Learn how combining threat intelligence and vulnerability management creates a modern approach to risk reduction and how Recorded Future integrates bo...
Evaluating digital risk intelligence platforms? Learn the 5 essential capabilities you should consider in order to protect your brand, assets, and att...
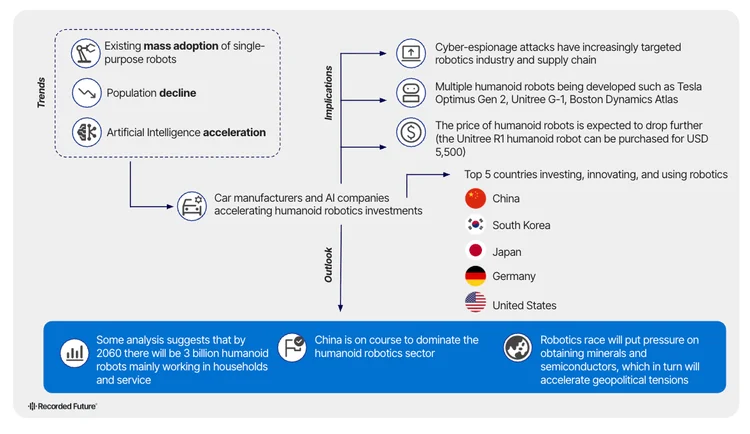
Humanoid robots are arriving faster than anyone expected. Discover the hidden risks, global power shifts, and breakthroughs shaping the future — befor...

Discover how threat intelligence automation from Recorded Future empowers security teams with real-time insights, faster response, and greater efficie...
Are you sure you want to sign out?