
Look What You Made Us Patch: 2025 Zero-Days in Review
Written by: Casey Charrier, James Sadowski, Zander Work, Clement Lecigne, Benoît Sevens, Fred Plan Executive Summary Google Threat Intelligence Group...
Construction industry and development projects

Written by: Casey Charrier, James Sadowski, Zander Work, Clement Lecigne, Benoît Sevens, Fred Plan Executive Summary Google Threat Intelligence Group...
![I tried Nothing Phone (4a) Pro – where did all the transparency go? [Gallery]](/articles/3836/E8nKXI0SNOmxgcFbXVKQ8epVRnhE0DA0.webp)
The Nothing Phone (4a) Pro has arrived and, while it looks like a really solid upgrade on paper, the new device largely ditches the transparent design...

Nothing has just launched its new Phone (4a) and Phone (4a) Pro with a slightly higher starting price, but some major upgrades across the board. more…
The Rust team is happy to announce a new version of Rust, 1.94.0. Rust is a programming language empowering everyone to build reliable and efficient s...

Your afternoon lineup of the best Android game and app awaits below, including titles like Rush Rally 3, Rush Rally Origins, The Macabre Journey: Dark...
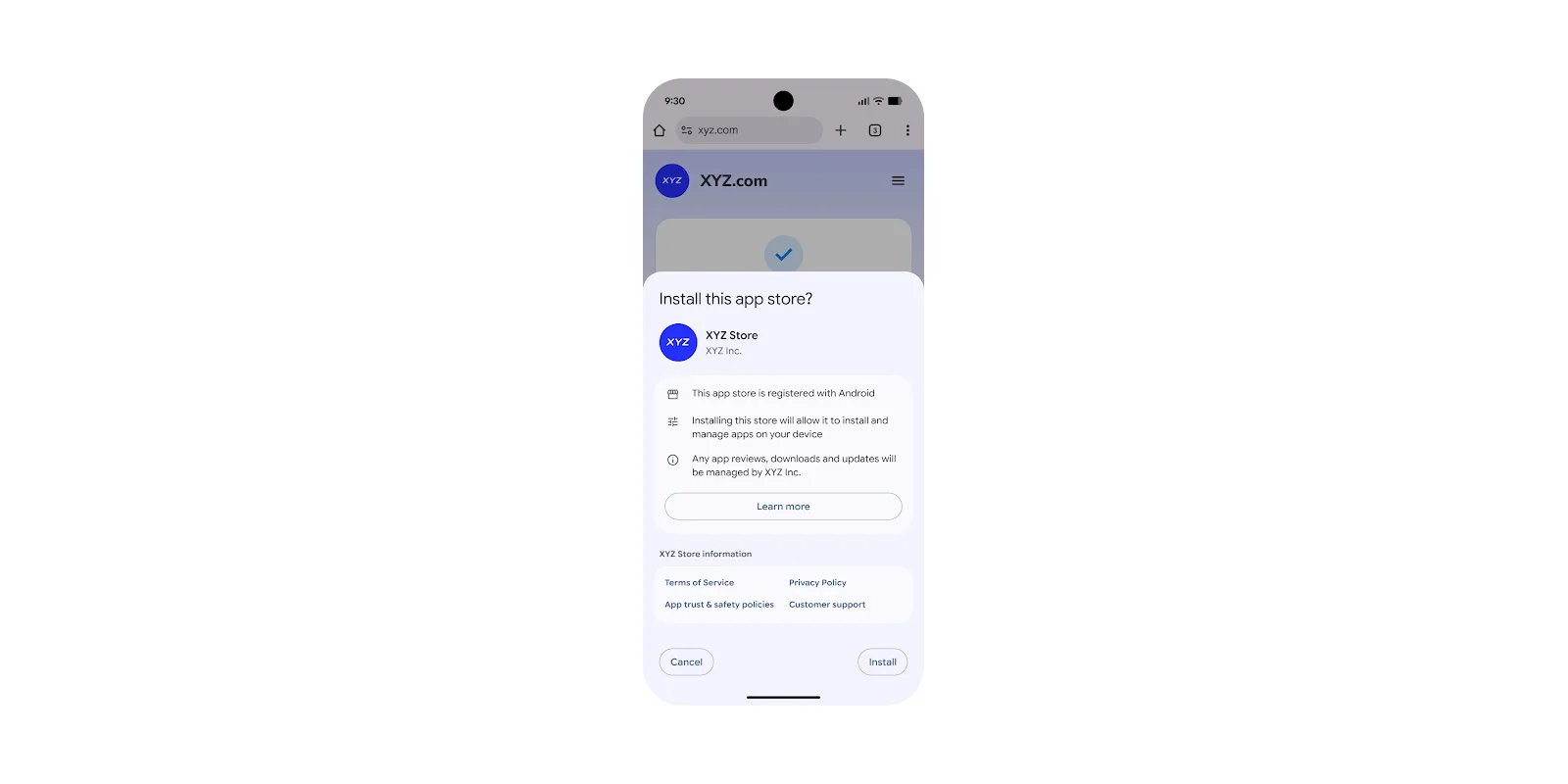
The long-running Google vs Epic Games dispute has finally come to an end, with Google today announcing new changes to Android that include better supp...

Samsung’s new Galaxy S26 series has arrived, but without the built-in magnets you’ll find on the latest iPhones or Google’s Pixel phones. Don’t fret,...

Today, we’re announcing the general availability of H4D VMs, our latest high performance computing (HPC)-optimized VM, powered by the 5th Generation...

A car you can talk to has been a longstanding dream, whether as the basis for television shows or more recent smartphone integrations. One way of ach...

To achieve Level 4 and Level 5 autonomous network operations (ANO), the telecommunications sector is increasingly turning to AI to build self-healing,...
Last year, Google Cloud unveiled the Autonomous Network Operations framework, a comprehensive blueprint designed to help Communication Service Provide...

The complexity of modern telecommunications is exploding. Communication Service Providers (CSPs) are no longer managing static, isolated networks; the...

The telecommunications industry has reached a critical tipping point. Traditional, on-premises-heavy data center models are struggling under the weigh...

Latin America's threat landscape is evolving fast — and reactive defense is no longer enough. PIX fraud, ransomware, and targeted attacks are outpacin...

Hello, Rust community! Once again, the survey team is happy to share the results of the State of Rust survey, this year celebrating a round number - t...

Recorded Future is expanding its payment fraud prevention capabilities through a partnership with CYBERA, the industry leader in detecting and verifyi...
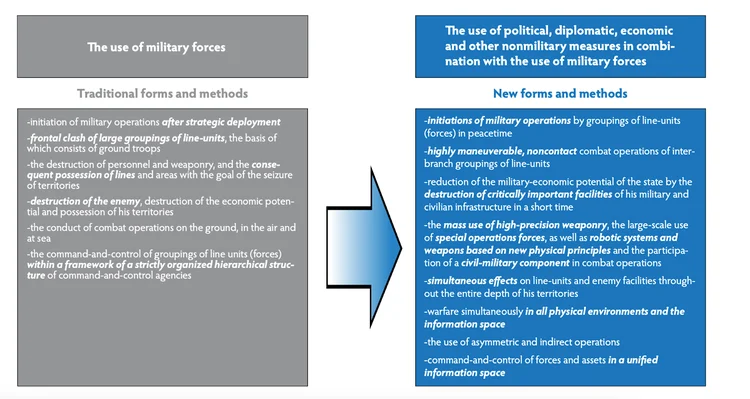
Russia is escalating its hybrid warfare against NATO into a coordinated, full-scale campaign blending cyber attacks, sabotage, and influence operation...

January 2026 saw 23 actively exploited CVEs, including APT28’s Microsoft Office zero-day and critical auth bypass flaws impacting enterprise systems.
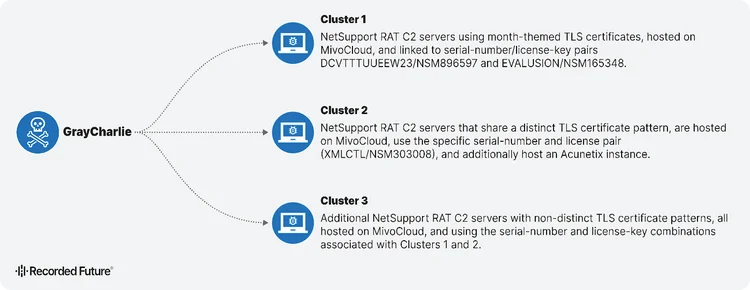
GrayCharlie turns compromised WordPress sites into malware delivery machines. Discover how this threat actor chains fake browser updates and ClickFix...
Learn how network intelligence gives security teams control over threat investigation with global visibility—no more drowning in generic, passive thre...
Are you sure you want to sign out?