
The rise of the autonomous network: How GraphML is redefining telecom operations
The complexity of modern telecommunications is exploding. Communication Service Providers (CSPs) are no longer managing static, isolated networks; the...
Real estate investment opportunities

The complexity of modern telecommunications is exploding. Communication Service Providers (CSPs) are no longer managing static, isolated networks; the...

The telecommunications industry has reached a critical tipping point. Traditional, on-premises-heavy data center models are struggling under the weigh...

Latin America's threat landscape is evolving fast — and reactive defense is no longer enough. PIX fraud, ransomware, and targeted attacks are outpacin...

Recorded Future is expanding its payment fraud prevention capabilities through a partnership with CYBERA, the industry leader in detecting and verifyi...

January 2026 saw 23 actively exploited CVEs, including APT28’s Microsoft Office zero-day and critical auth bypass flaws impacting enterprise systems.
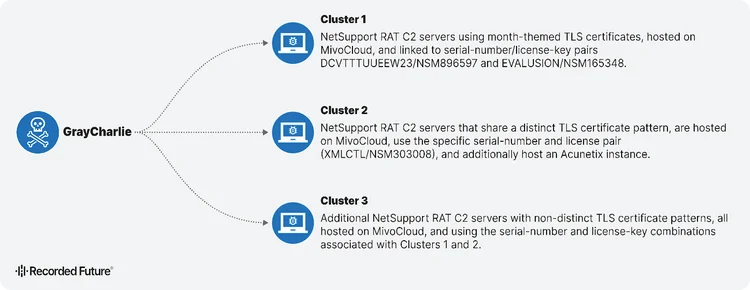
GrayCharlie turns compromised WordPress sites into malware delivery machines. Discover how this threat actor chains fake browser updates and ClickFix...
Learn how network intelligence gives security teams control over threat investigation with global visibility—no more drowning in generic, passive thre...
Discover how Autonomous Threat Operations reduces 27 manual steps to as few as 5 largely automated ones, delivering the speed, scale, and effectivenes...
This article explores how Recorded Future served as Customer Zero for Autonomous Threat Operations, testing the new solution within our own SOC to val...
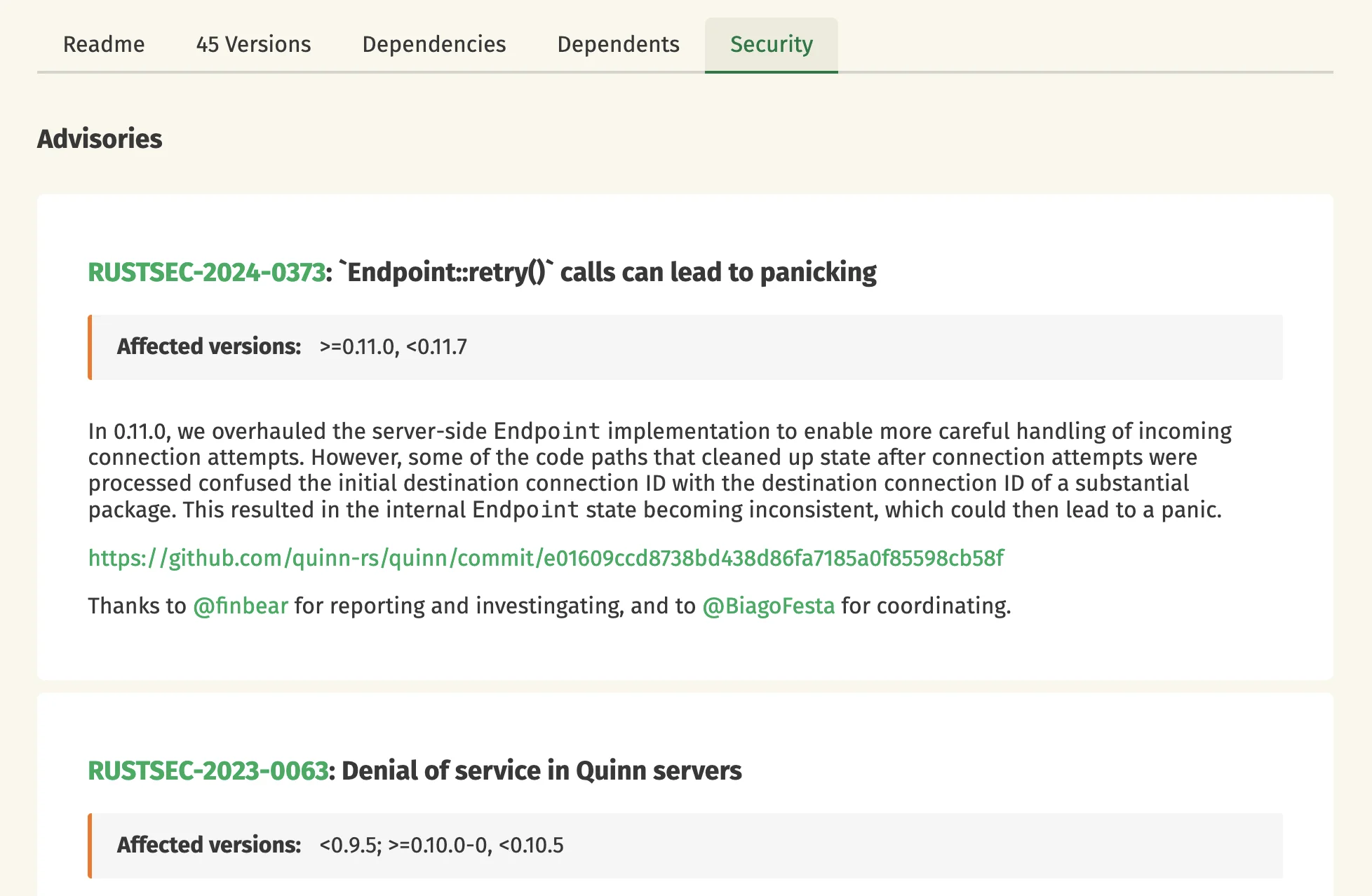
Time flies! Six months have passed since our last crates.io development update, so it's time for another one. Here's a summary of the most notable cha...

Understand the future of threat and vulnerability management (TVM). Learn what TVM is, why traditional tools fail, and how intelligence is essential i...
This is another post in our series covering what we learned through the Vision Doc process. In our first post, we described the overall approach and w...

December 2025 saw a 120% surge in critical CVEs, with 22 exploited flaws and React2Shell (CVE-2025-55182) dominating threat activity across Meta’s Rea...

Threat intelligence practitioners from Global Payments, Adobe, and Superhuman reveal how mature CTI programs transform data overload into strategic bu...
Ransomware groups made less money in 2025 despite a 47% increase in attacks, driving new tactics: bundled DDoS services, insider recruitment, and gig...

The Rust project is currently working towards a slate of 41 project goals, with 13 of them designated as Flagship Goals. This post provides selected u...
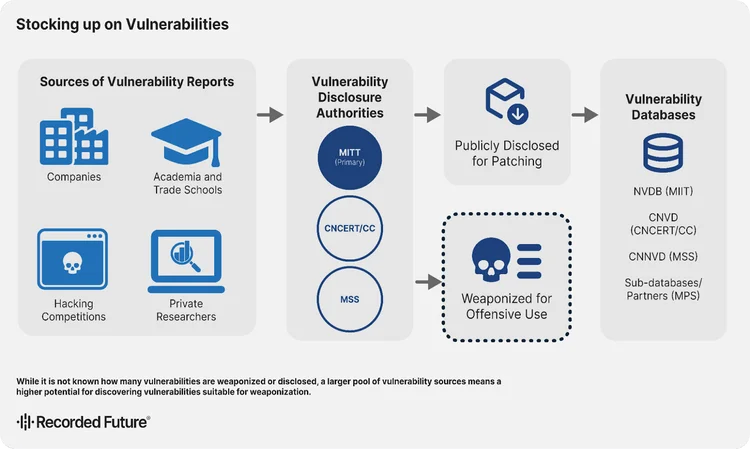
China is consolidating cyber power through zero-days. Explore how state control of vulnerabilities enables long-term strategic advantage.
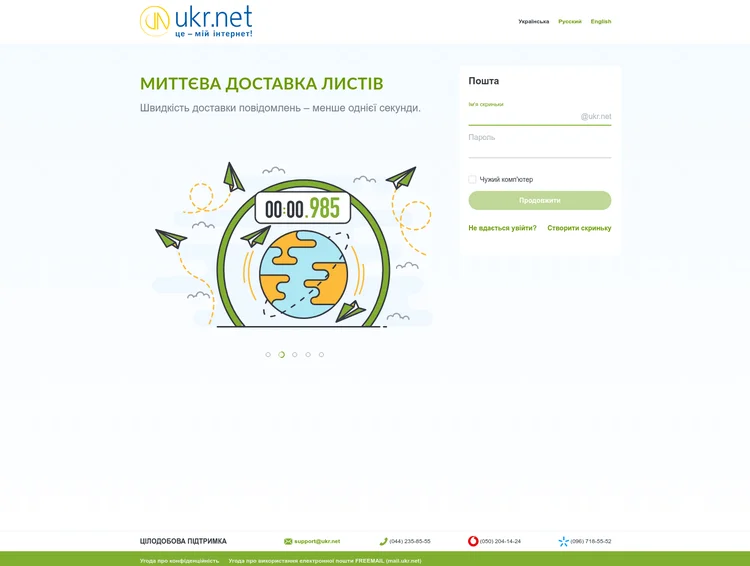
Discover how Russia’s BlueDelta targets UKR.NET users with advanced credential-harvesting campaigns, evolving tradecraft, and multi-stage phishing tec...

Top enterprise threat intelligence trends for 2026: AI-augmented CTI, unified platforms, workflow integration, data fusion, budgets, ROI, and maturity...

Explores Palestine Action’s post-designation global network, tactics, and targets, and evaluates key physical risks and mitigations for organizations.
Are you sure you want to sign out?