
The rise of the autonomous network: How GraphML is redefining telecom operations
The complexity of modern telecommunications is exploding. Communication Service Providers (CSPs) are no longer managing static, isolated networks; the...
Real estate market trends and analysis

The complexity of modern telecommunications is exploding. Communication Service Providers (CSPs) are no longer managing static, isolated networks; the...

The telecommunications industry has reached a critical tipping point. Traditional, on-premises-heavy data center models are struggling under the weigh...

Hello, Rust community! Once again, the survey team is happy to share the results of the State of Rust survey, this year celebrating a round number - t...
Discover how Autonomous Threat Operations reduces 27 manual steps to as few as 5 largely automated ones, delivering the speed, scale, and effectivenes...

Stop ransomware before encryption begins. Learn how intelligence-driven detection tools can help identify precursor behaviors and reduce false positiv...

Threat intelligence practitioners from Global Payments, Adobe, and Superhuman reveal how mature CTI programs transform data overload into strategic bu...

Insikt Group reveals how GRU-linked BlueDelta evolved credential-harvesting campaigns targeting government, energy, and research organizations across...
Explore digital threat detection tools and learn best practices to identify, analyze, and neutralize digital threats before they impact your business.
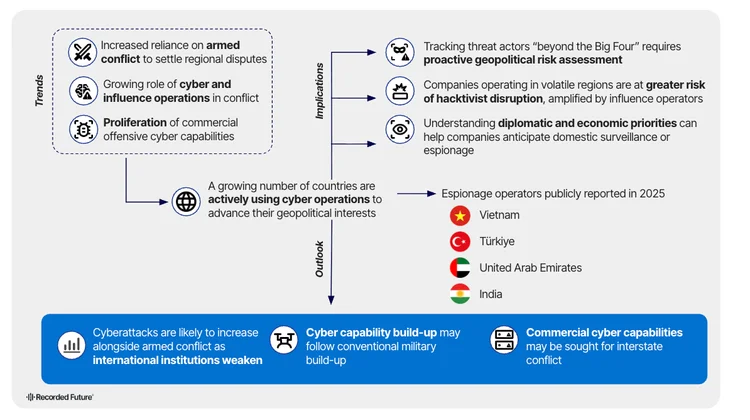
Offensive cyber operations are spreading beyond the Big Four. Discover how regional conflicts are driving new state-linked cyber threats.

A $0 card test signaled a Chinese state-linked cyberattack on Anthropic’s AI platform. Learn how card-testing fraud intelligence spots nation-state op...
Explore 5 third-party risk examples, from vendor data breaches to supply chain attacks and learn how third-party risk management can prevent cyberatta...

Discover how converged threat intelligence protects executives from deepfakes, doxxing, and cyber-enabled physical threats with Recorded Future.

Discover how law firm breaches expose decades of M&A intelligence, client data, and privileged strategy—and how to reduce cascading vendor risk be...

Learn what advanced threat intelligence maturity really means and how to close the gap between current capabilities and predictive, autonomous operati...
Uncover Intellexa’s global corporate web powering Predator spyware, front companies, and expanding targeting from civil society to executives worldwid...

A grounded look at AI malware: most threats sit at low maturity levels, with no verified autonomous BYOAI attacks. Learn what’s real, what’s hype, and...

Discover how threat intelligence automation from Recorded Future empowers security teams with real-time insights, faster response, and greater efficie...

Explore the latest third-party risk statistics and learn how data-driven, continuous monitoring for third-party risk assessments can protect your supp...

The former design lead at Apple has teamed up with Sam Altman’s artificial intelligence company.

The Razer Huntsman V3 Pro Tenkeyless is a mechanical keyboard that you can make (almost) entirely your own, even without macOS support for its Synapse...
Are you sure you want to sign out?