
Practitioners Reveal What Makes Threat Intelligence Programs Mature
Threat intelligence practitioners from Global Payments, Adobe, and Superhuman reveal how mature CTI programs transform data overload into strategic bu...

Threat intelligence practitioners from Global Payments, Adobe, and Superhuman reveal how mature CTI programs transform data overload into strategic bu...

December 2025 saw a 120% surge in critical CVEs, with 22 exploited flaws and React2Shell (CVE-2025-55182) dominating threat activity across Meta’s Rea...

Stop ransomware before encryption begins. Learn how intelligence-driven detection tools can help identify precursor behaviors and reduce false positiv...

Understand the future of threat and vulnerability management (TVM). Learn what TVM is, why traditional tools fail, and how intelligence is essential i...
This article explores how Recorded Future served as Customer Zero for Autonomous Threat Operations, testing the new solution within our own SOC to val...
Discover how Autonomous Threat Operations reduces 27 manual steps to as few as 5 largely automated ones, delivering the speed, scale, and effectivenes...
Learn how network intelligence gives security teams control over threat investigation with global visibility—no more drowning in generic, passive thre...
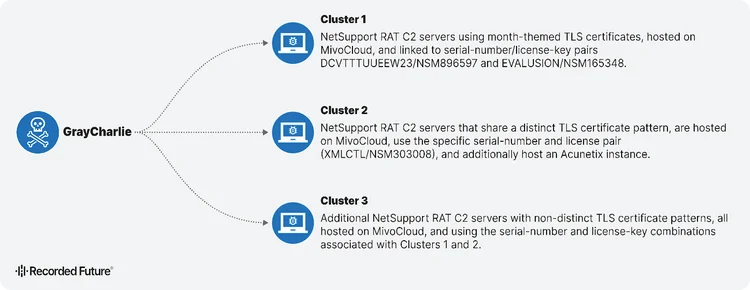
GrayCharlie turns compromised WordPress sites into malware delivery machines. Discover how this threat actor chains fake browser updates and ClickFix...
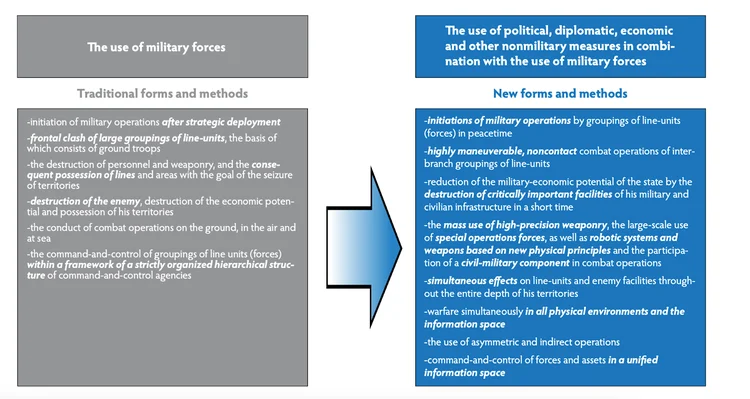
Russia is escalating its hybrid warfare against NATO into a coordinated, full-scale campaign blending cyber attacks, sabotage, and influence operation...

January 2026 saw 23 actively exploited CVEs, including APT28’s Microsoft Office zero-day and critical auth bypass flaws impacting enterprise systems.

Recorded Future is expanding its payment fraud prevention capabilities through a partnership with CYBERA, the industry leader in detecting and verifyi...

Latin America's threat landscape is evolving fast — and reactive defense is no longer enough. PIX fraud, ransomware, and targeted attacks are outpacin...

Samsung’s new Galaxy S26 series has arrived, but without the built-in magnets you’ll find on the latest iPhones or Google’s Pixel phones. Don’t fret,...
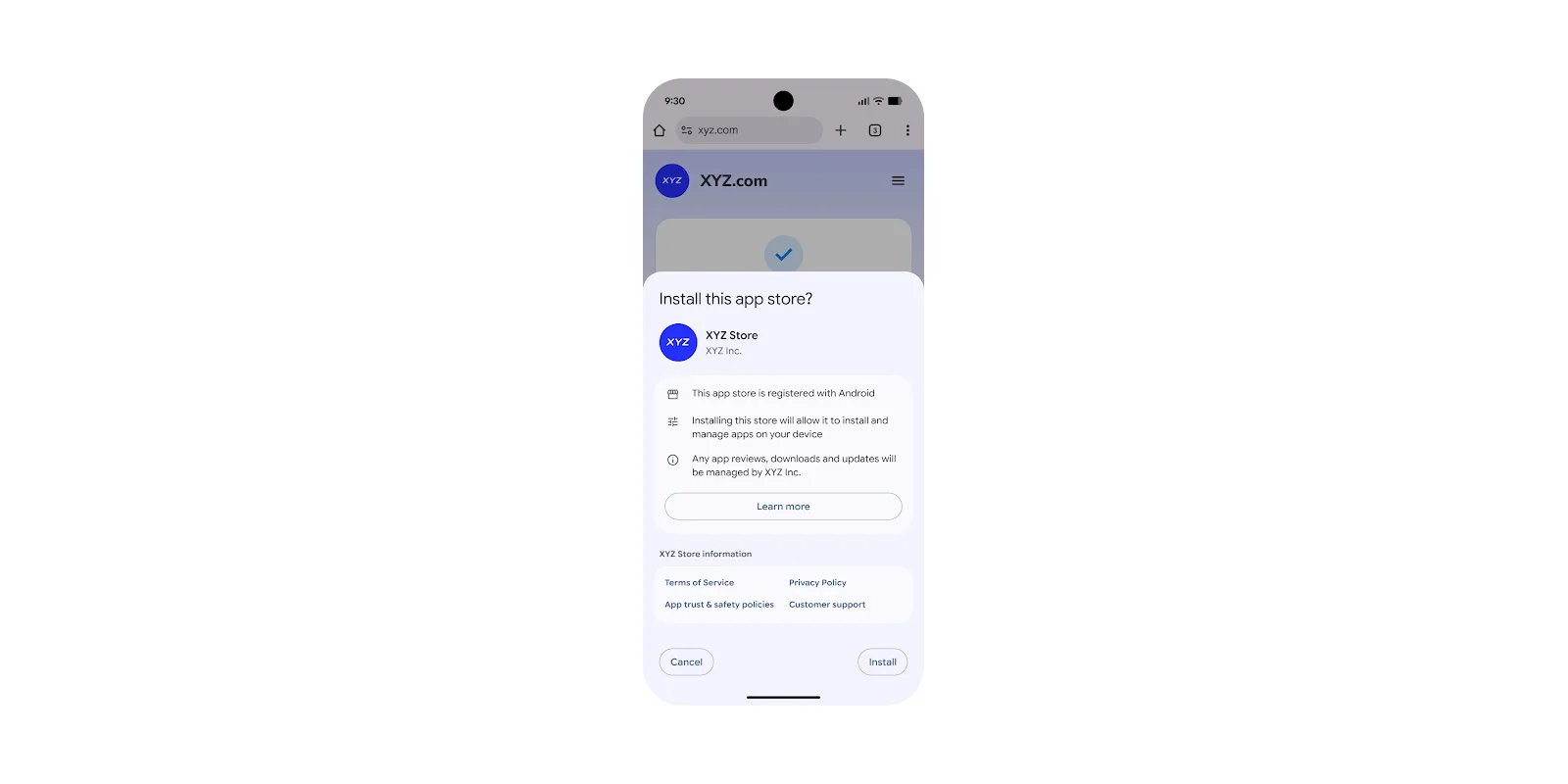
The long-running Google vs Epic Games dispute has finally come to an end, with Google today announcing new changes to Android that include better supp...

Your afternoon lineup of the best Android game and app awaits below, including titles like Rush Rally 3, Rush Rally Origins, The Macabre Journey: Dark...
Are you sure you want to sign out?